CV25 Architecture – Future of Sovereign Edge AI
In the landscape of modern cyber-warfare, data is the new uranium. The reliance on foreign-manufactured surveillance equipment creates a strategic vulnerability—a “Trojan Horse” inside critical infrastructure.
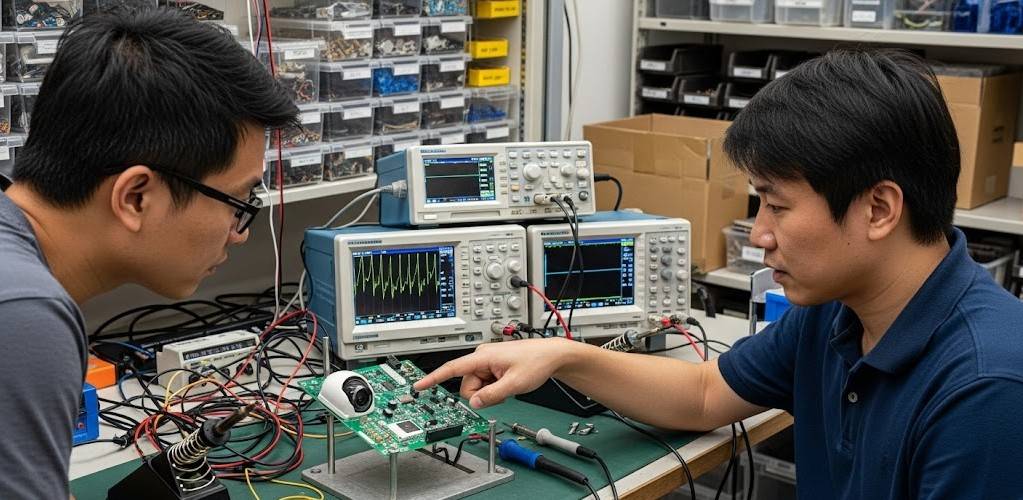
At MK Vision – Pavana, we do not just assemble cameras; we master the core technologies. Introducing the CV25 Sovereign Series—a vision platform built on the philosophy of “Security by Design,” ensuring that your data remains strictly yours.
With 82% Local Content and 100% Control over the embedded software stack, we offer what off-the-shelf solutions cannot: Absolute Peace of Mind.
PAVANA DEFENSE
Secure Systems Div.
SOVEREIGN
EDGE AI
Redefining National Security.
Absolute Control. 82% Local Content.
Q: In a world of “Chip Wars” and supply chain attacks, how does Pavana guarantee hardware integrity?
A: 82% Local Content & 7 Core Technologies Mastered.
Trust must be verifiable. Unlike competitors who relabel imported hardware (OEM), Pavana owns the full stack. We have mastered 7 Core Technologies, ranging from mechanical design and PCB layout to the deepest layers of embedded software.
By achieving a localization rate of 82%, we drastically reduce the risk of hardware backdoors. We control the supply chain, ensuring that every component on the board is vetted, verified, and secure. This is not just manufacturing; it is Digital Sovereignty.
Q: Generic AI models generate false positives. How does Pavana solve this for critical security?
A: “The AI Factory” – Bespoke Deep Learning.
Security threats are context-specific. A generic model trained on a public dataset is insufficient for recognizing specific threats in a Vietnamese context.
Pavana operates as an “AI Factory.” We do not simply deploy; we tailor. We develop Bespoke Deep Learning models optimized specifically for the Ambarella CV25 chip. Whether it is detecting unauthorized personnel in a power plant or identifying license plates in complex traffic, our models deliver real-world precision that generic solutions fail to achieve.
Q: How does the system prevent unauthorized code execution or data theft?
A: Active 3-Tier Security Architecture.
We implement a defense-in-depth strategy anchored in hardware:
- Secure Boot: We utilize the CV25’s hardware root of trust to verify the digital signature of the bootloader. If the software has been tampered with, the device simply will not start.
- Data Encryption: All data, whether at rest (storage) or in transit (streaming), is encrypted using military-grade AES standards.
- Hardware-Level Privacy: Critical keys are stored in isolated secure enclaves (TrustZone), inaccessible to the main operating system.
Q: In emergency handling, every millisecond counts. What is the system’s reaction time?
A: Sub-500ms Instant Response.
Cloud analytics introduce latency—the enemy of security. By processing data at the source (Edge Computing), the Pavana CV25 platform achieves an inference latency of under 500 milliseconds.
This Instant Response capability allows security teams to react to threats as they happen, not after the data has traveled to a server and back. In critical infrastructure protection, this speed saves assets and lives.